Training videos are one of the most efficient and engaging ways to share knowledge across an organization. Whether you’re recording new employee training, communicating a new company policy change, or launching a cybersecurity awareness training module, video can communicate information faster and more clearly than static documentation.
However, there’s an important catch: these videos are usually made in-house and often contain sensitive company information, proprietary visuals, or personal data, and that can introduce serious security risks if not mitigated properly.
Security compliance is not optional. For example, anything from HIPAA compliance and GDPR regulations to internal information security standards, even small lapses in secure video creation, can lead to serious complications. Data breaches, phishing exposure, and insider threat scenarios are all too real and can happen anywhere from whole internal wikis to specific standard operating procedures (SOPs).
Luckily, staying compliant isn’t a hard process. With a few small best practices and the right tools, you can safeguard your content while keeping your training platform efficient, scalable, and aligned with cybersecurity best practices.
Common risks in training videos that impact compliance
Even the most well-crafted and intentional video training content can introduce unforeseen vulnerabilities. The following sections are three of the most common compliance and security risks found in everyday training videos, along with tips on how to spot and prevent them from the get-go.
Accidental exposure of sensitive data
A very frequent risk in training videos is the unintentional capture of sensitive information. It’s super easy to overlook what appears on-screen during a screen recording. Dashboards, email inboxes, Microsoft Teams chats, browser tabs, or even file names can reveal more than intended.
For example, a quick product walkthrough may include a brief glimpse of a confidential file you thought you closed, or an email tab may flash a client’s personal identifiable information (PII), an internal SOP, or login credentials. These small, seemingly inconsequential exposures can escalate into serious data breaches or compliance issues if the screen recording is shared with the wrong people.
When building training content–even if it is a quick tutorial–it’s essential to stay aware of everything visible on your desktop. An easy way to avoid any issues is to open a new, blank desktop and only open the content you need in your screen recording. That way, you know exactly what is visible on screen, and the chances of accidental exposure are minimized.
Lack of access to control when hosting
Another major vulnerability comes from where and how training videos are hosted. Uploading a compliance training video to a public platform or sharing it via a non-restricted link can inadvertently expose internal content to unauthorized viewers, including competitors, hackers, or bots.
You need a secure hosting platform. Screencast, which is directly linked to Camtasia, is a secure, cloud-based hosting platform, including access phrase protection for individual videos and video collections. This type of security is secure yet easy for users who need to watch the videos without hassle.
Failure to follow industry-specific regulations
In highly regulated sectors, like healthcare, finance, or education, you need to align your content creation, storage, and distribution with frameworks like:
- HIPAA for handling patient data
- GDPR for personal data within the EU
- Company-specific IT and cybersecurity policies.
Non-compliance is unethical and can lead to fines, reputational damage, or worse. By respecting your employees’ and clients’ trust, you can avoid a myriad of issues.
Best practices to create compliant, secure training videos
Thankfully, risk management isn’t a complex process. Start by building a few smart compliance programs into your training program, and choose tools that support information security by design.
Use screen capture tools that support secure editing
Not all screen capture tools are created equal. To protect your content, choose solutions that allow you to blur, redact, crop, or otherwise remove sensitive content before finalizing the video.
TechSmith’s tools make this super easy.
Camtasia
Camtasia is ideal for more in-depth training videos. This all-in-one screen recorder and video editor offers precise control over video and audio tracks, so you can easily edit out sensitive information without re-recording an entire module.
In addition to cutting out specific screen content, you can also blur it out or add a customizable shape over screen content to obscure it.
Faster video creation with Rev
Make videos as easy as click, click, done! Camtasia Rev is so fast it’s like magic!
Learn More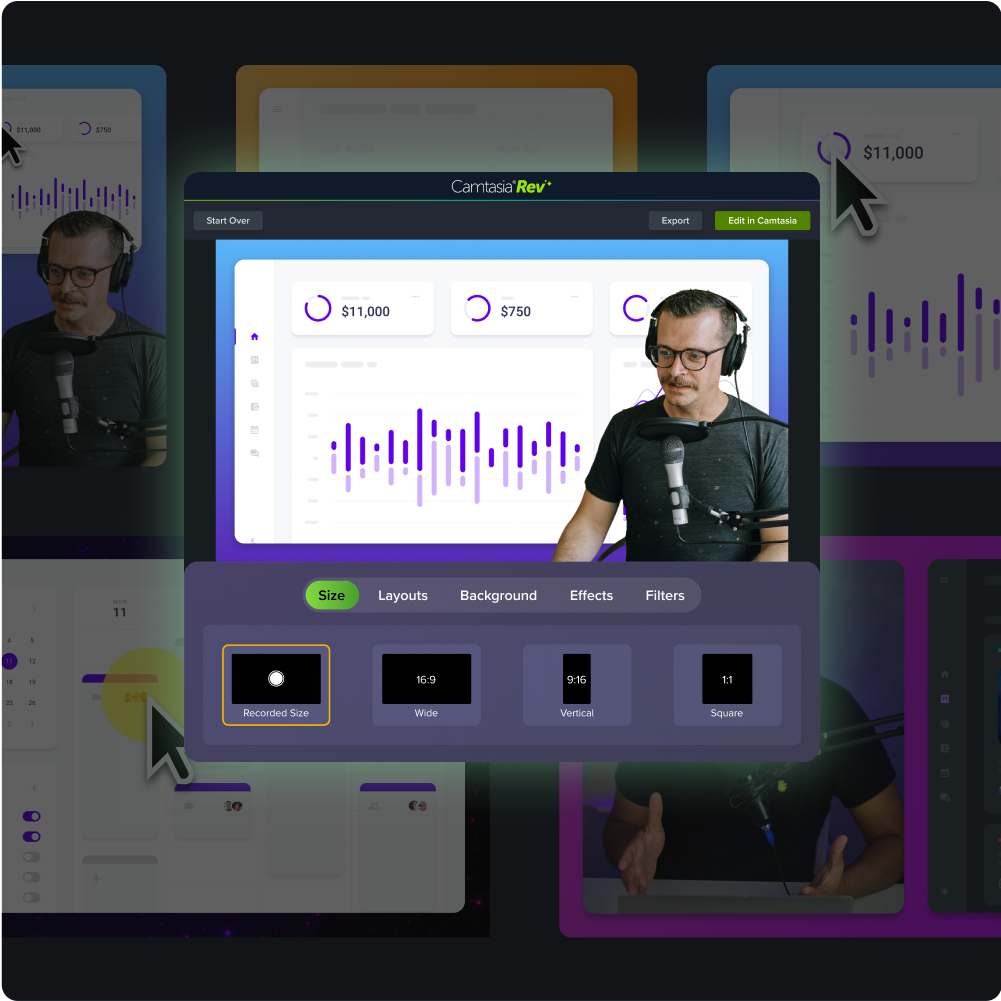
Snagit
Snagit is a great tool for quick screen captures. While not primarily a video tool, screen captures are just as important in training content. Snagit’s image editor includes smart redact, which automatically detects and blacks out PII for you. Usernames, client names, email addresses, social security numbers, and card information are all removed with the click of a toggle.
You can also select information or images with the select tool and press the delete key on Mac or the backspace key on Windows to make it disappear. Snagit will automatically fill in the background to match as best as possible for a seamless look.
Set compliance file access and sharing permissions
Once your video is created, the next step is to share it securely. Use hosting platforms that allow you to do some or all of the following:
- Enable password protection (most important!)
- Internal audience viewing only
- Set user-level permissions
Avoid sending unlisted YouTube links or uploading training content to platforms that don’t put security at the forefront.
Document and organize videos for internal search and governance
Keeping training content organized is a key component of compliance and audit-readiness.
Screencast, TechSmith’s hosting option that is linked to Snagit and Camtasia, allows you to create collections to group videos by audience, sensitivity level, or project type so you can easily figure out who can view what and when. This structured system also makes it easy to locate content when you need it to make any updates.
Incorporating tagging strengthens your organizational system and helps maintain training continuity over time.
How secure training videos benefit your team
Secure video training is about compliance and security, and it also strengthens your entire organization. When teams prioritize security compliance, it builds trust, improves agility, and makes scaling easier.
Prevents data leaks and reputational damage
Training videos often contain a wealth of information, and without proper controls, this can become a goldmine for people who are trying to access sensitive information.
When your team applies cybersecurity best practices like redaction, secure hosting, and permission-based access, your organization can stay one step ahead at all times.
Enables training at scale without security trade-offs
Distributed workforces, remote employees, and global operations all rely on scalable, self-paced learning. However, scale should never come at the cost of security.
When you integrate compliance into your training program from the start, you can expand your training program with confidence. There are no worries about certain videos being reused to make other training videos because it is secure to begin with. Everyone can access the content they need without increasing security risks.
Supports long-term content reuse
A well-designed compliance training video can and should be reusable. When videos are scrubbed of sensitive information and properly permissioned, they can live in your knowledge base, be shared with new employees, or included in future modules without needing to start from scratch.
This is especially valuable for foundational topics like cybersecurity threats, phishing scams, or product tutorials. Over time, your team saves effort, reduces content duplication, and maintains consistent messaging across the entire organization.
Protect your training content without slowing down
You may think that security compliance will add friction to your training program, but that doesn’t have to be the truth. With the right tools and thoughtful habits, your organization can create, share, and manage training videos that are effective and secure.
TechSmith’s suite of tools should be the foundation of your training content toolbox. Snagit, Camtasia, and Screencast are built with information security in mind. All together, they offer screenshotting options, screen recordings, editing tools, and a hosting platform that make your content more secure. Blur sensitive information in images and videos, and share passphrase-protected files in organized folders with TechSmith’s seamless integration between tools.
Explore all of TechSmith’s products and discover how your team can create clear, secure content from day one.





Share